What if your software isn’t as secure as you think? As cyber threats escalate, understanding the implications of quantum-safe solutions becomes crucial for Americans. If we’re not careful, the stakes could cost us billions in lost data and trust.
1,000,000. That’s the estimated number of ransomware attacks occurring globally each year. As businesses scramble to strengthen their defenses, a new player has emerged that claims to be quantum-safe. The Kyber ransomware family, first spotted in September 2025, raises serious questions about the future of cybersecurity in a world that’s rapidly approaching the quantum computing frontier. How will this development reshape your understanding of data security and the tools you rely on?
What’s Actually Happening

The Kyber ransomware family has gained attention for its unique claim of utilizing quantum-safe encryption through a mechanism known as ML-KEM (Module Lattice-based Key Encapsulation Mechanism). This encryption method is touted as resistant to the cracking capabilities of quantum computers, which are poised to revolutionize the world of cryptography. The National Institute of Standards and Technology (NIST) has been actively working on standardizing post-quantum cryptographic algorithms, with ML-KEM being one of the frontrunners.
In its early stages, the Kyber ransomware was noted for aggressively marketing itself as quantum-safe, attracting the interest of cybersecurity experts and businesses alike. By employing this novel encryption method, Kyber attempts to enhance its credibility in a landscape filled with traditional ransomware threats. This shift toward quantum-safe methodologies represents a new frontier in cybercrime, potentially complicating how organizations defend against ransomware attacks.
The Bigger Picture

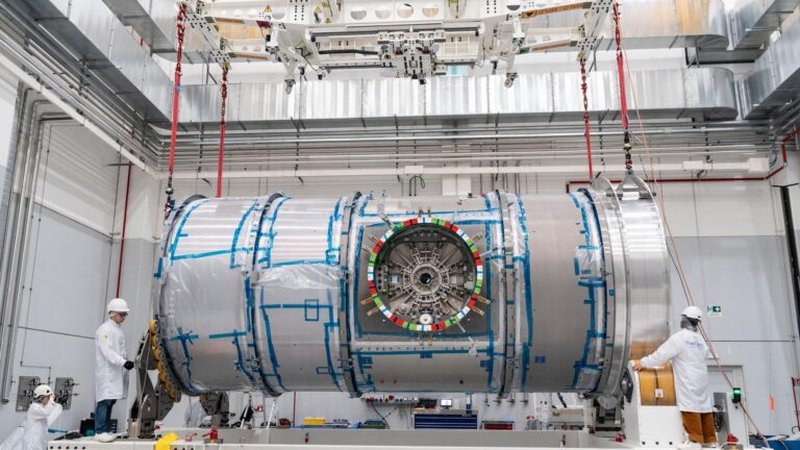
Video: What is Quantum Safe?
Shifting Paradigms in Cybersecurity
The reality is that many businesses may not fully grasp the implications of quantum-safe ransomware. Most coverage highlights the immediate threat but misses the deeper shifts happening in cybersecurity. Here’s how this all unfolds: (per coverage from MIT Technology Review)
Stage 1 — The immediate, direct effect: Organizations that fall victim to Kyber ransomware face immediate data loss and operational disruption. According to cybersecurity experts, the average ransom payment has soared to $300,000 in 2025, a clear financial risk for businesses of any size. Victims may also incur additional costs in recovery efforts, legal fees, and potential regulatory fines.
Stage 2 — Secondary ripple effects: As businesses contend with the fallout from a Kyber attack, supply chains may also feel the strain. Companies across various sectors, including healthcare and finance, depend on software that controls sensitive data. If these businesses face ransomware attacks, it could create a domino effect, impacting partners and customers, ultimately leading to lost revenue and even customer trust.
Stage 3 — Long-term structural consequence: The emergence of quantum-safe ransomware could push organizations to rethink their entire cybersecurity strategies. As cyber threats evolve, companies may need to adopt a more proactive approach to cryptography, moving past traditional methods that are vulnerable to quantum decryption. This could mean increased investments in new technologies and training for employees, fundamentally altering the landscape of cybersecurity.
Real-World Case Study
Consider the case of Colonial Pipeline, which suffered a major ransomware attack in May 2021. The attack forced the company to halt operations, resulting in gas shortages across the Eastern United States. The resulting ransom payment of $4.4 million was a staggering wake-up call for businesses nationwide. Fast forward to 2025, and imagine a scenario where a company using traditional encryption methods falls victim to Kyber ransomware. The costs could multiply exponentially—not just from the ransom itself but also in terms of damage to reputation and operational downtime. This historical parallel underscores an urgent need to adapt to new threats as they emerge.
What This Means for America

For American consumers and businesses, the implications are profound. Every successful ransomware attack doesn’t just jeopardize individual companies; it creates a ripple effect that can impact entire markets. If companies are forced to pay steep ransoms, it could drive prices higher for consumers as businesses pass on the costs. (according to Wired)
Moreover, the urgency for businesses to adopt quantum-safe technologies is more critical than ever. As organizations invest in these solutions, the cybersecurity industry is likely to see growth. This could ultimately lead to job creation in the tech sector. However, this also means that companies that lag behind risk losing market competitiveness and exposing themselves to catastrophic data breaches.
In the tech race against cyber threats, it’s vital to highlight who stands to gain and who might suffer. Cybersecurity firms specializing in quantum-safe technologies will likely benefit. In contrast, companies stuck in outdated systems may face steep penalties from regulators and damage to their reputations. You can’t overlook this growing divide.
What This Means for You

What should you take away from this? If you’re a business owner, reconsider your cybersecurity approach today. You need to ask yourself, “Are we prepared for the quantum future?” The software you rely on could be vulnerable. Now’s the time to conduct an audit of your current cybersecurity systems, focusing on data encryption methods.
If you’re a consumer, be aware of how these cyber threats impact services you rely on daily. A disruption in the supply chain or data breach at a major corporation could affect everything from your banking to healthcare services. Keep an eye on the companies you trust; ensure they’re investing in robust cybersecurity measures.
As cyber threats evolve, the emergence of quantum-safe software raises critical questions about digital security in a post-quantum world. With quantum computing poised to break traditional encryption methods, organizations are under pressure to adopt encryption solutions designed to withstand quantum attacks. However, the recent claims from Kyber Ransomware highlight the growing divide between effective quantum-resistant algorithms and those merely marketed as quantum-safe. As businesses navigate this complex landscape, the reliability of cryptographic protocols becomes paramount to safeguarding sensitive data from increasingly sophisticated threats. (as reported by Reuters Technology)
Key Takeaways
- 1 million ransomware attacks happen annually, highlighting a growing cybersecurity crisis.
- The Kyber ransomware family uses ML-KEM, a quantum-safe encryption method.
- The average ransom payment soared to $300,000 in 2025.
- Organizations must rethink their cybersecurity strategies in light of evolving threats.
- Cybersecurity firms specializing in quantum-safe technologies are set to grow.
- Stay informed about the cybersecurity practices of companies you engage with.
- Investing in quantum-safe technologies now could save businesses from future ransomware costs.
What Happens Next
In the next 30 to 90 days, watch for increasing scrutiny on organizations that fail to adopt quantum-safe technologies. Regulatory bodies may begin pushing for standards that require businesses to upgrade their cybersecurity protocols. Moreover, expect to see a surge in the development of new software aimed at mitigating quantum threats. The kicker is that companies that lag in adapting could face not only cyber risks but also legal repercussions.
The writing’s on the wall: Adapt or become a statistic.
FAQs: Clarifying Common Concerns about Quantum-Safe Ransomware
- What is quantum-safe ransomware? Quantum-safe ransomware uses encryption methods that are designed to be secure against potential future quantum computing threats.
- How does ML-KEM work? ML-KEM employs mathematical problems based on lattices, which quantum computers do not solve more efficiently than classical computers.
- What should businesses do to protect themselves? Organizations should audit their security measures and consider adopting quantum-safe encryption technologies.
- How can consumers be affected? Disruptions caused by ransomware can impact services, leading to downtime and potential loss of sensitive data.
- Are all encryption methods at risk from quantum computing? Traditional methods like RSA and elliptic curve cryptography are vulnerable; thus, businesses should transition to post-quantum encryption.
James Park’s Verdict
What nobody is asking is why organizations are investing in post-quantum cryptography when there’s no immediate threat. Sure, we should be preparing for quantum computing, but wouldn’t it make more sense to prioritize solutions that address current vulnerabilities?
This situation reminds me of how European countries reacted to cyber threats compared to those in the U.S. While the U.S. often scrambles to react, countries like Estonia have taken proactive measures to fortify their digital infrastructure. If Europe can be ahead of the curve in cybersecurity, why can’t the software industry focus on immediate, practical solutions instead of flashy, theoretical breakthroughs?
In my view, we’re on the brink of a reality check. By mid-2027, I expect organizations to refocus their investments on software that addresses current security threats rather than chasing the elusive promise of quantum safety.
Frequently Asked Questions
What is quantum-safe software and how does it relate to Kyber ransomware?
Quantum-safe software refers to cryptographic algorithms designed to resist potential threats from quantum computers. Kyber ransomware claims its methods utilize such technology, suggesting enhanced security. However, experts debate the practical benefits of these claims, highlighting the need for thorough evaluation in real-world applications.
What are the implications of Kyber ransomware's claims about quantum-safe software?
The implications of Kyber ransomware's claims include increased awareness of quantum threats and the necessity for businesses to adopt post-quantum cryptography (PQC). While these claims may raise concerns, they also prompt discussions around the effectiveness and readiness of PQC solutions for real-world deployment.
Why do some experts doubt the practical benefits of quantum-safe software?
Experts doubt the practical benefits of quantum-safe software because many algorithms are still in early development stages, lacking extensive testing and real-world application data. Additionally, the urgency around quantum threats often overshadows necessary discussions about the effectiveness and feasibility of these solutions in current systems.



